Windows Kernel Rootkits: Techniques and Analysis
Bruce Dang
Dates
10-13 February 2020Capacity
18Price
4.000€(Early Bird 3.500€)
Course summary and expected outcome
This course is tailored for malware analysts, system developers, forensic analysts, incident responders, or enthusiasts who want to analyze Windows kernel rootkits or develop software for similar tasks. It introduces the Windows architecture and how various kernel components work together at the lowest level. It discusses how rootkits leverage these kernel components to facilitate nefarious activities such as hiding processes, ?les, network connections, and other common objects. As part of the analytical process, we will delve into the kernel programming environment; we will implement some kernel-mode utilities to aid our understanding.
After this class, you should have a systematic understanding of Windows kernel to analyze rootkits and develop kernel-mode utilities (or even products!) for your job. In addition, you will be able read and understand research on Windows kernel and related subjects. You will no longer feel intimiated by the kernel.
In our experience, practically all students are able to analyze kernel rootkits and develop drivers on their own at the end of the course. Most students have never written a driver before in their life and felt comfortable doing it after the third
day. Here are some examples of what some students accomplished: analyzed well-known kernel APTs, analyzed Windows PatchGuard, developed a driver to remap keys, researched into hypervisor development.
If you pay attention in class and do the exercises, you will end up discovering interesting ideas that can lead to original research.
Course prerequisites
No prior experience with Windows is required. However, the course primarily focuses on the analysis and development of Windows malicious kernel drivers. In order to get the most out of it, you need to have some C/C++ programming experience (you will be developing kernel mode drivers). If you are not comfortable with that, you can still understand the material and apply it to your daily job, however you might need to work extra hard in class.
Hardware and software requirements
You are expected to bring a laptop running Windows (preferrably Windows 10) as the host OS. We will be using virtual machines and snapshotting so ideally it would have an SSD drive and at least 8GB of RAM. Please install VMWare Workstation (30-day trial version is fine) on it.
The list of required software on the host is listed below. Make sure to install Visual Studio first, then SDK, then WDK.
- Visual Studio 2019. The edition does not matter. You can use the free Community Edition which can be downloaded from https://www.visualstudio.com/downloads/. Make sure to choose Desktop development with C++ during installation.
- SDK For Windows 10, version 1903. It can be downloaded from https://developer.microsoft.com/en-us/windows/downloads/windows-10-sdk
- WDK for Windows 10, version 1903. It can be downloaded from https://developer.microsoft.com/en-us/windows/hardware/windows-driver-kit
- WinDbg Preview. It can be downloaded from https://www.microsoft.com/en-us/store/p/windbg/9pgjgd53tn86. A Windows 10 host is required for this.
- IDA Pro with support for x64 binaries. The decompiler is not needed but would be useful.
- NASM. It can be downloaded from http://www.nasm.us
- ProcessHacker. It can be downloaded from https://wj32.org/processhacker/nightly.php . Use the nightly builds.
Class topics
- Machine architecture for kernel programmers
- CPU security features
- Windows kernel architecture
- Kernel components (Ps, Io, Mm, Ob, Se, Cm, etc.)
- System mechanisms
- Driver development
- Rootkit techniques
- Filter drivers
Bio
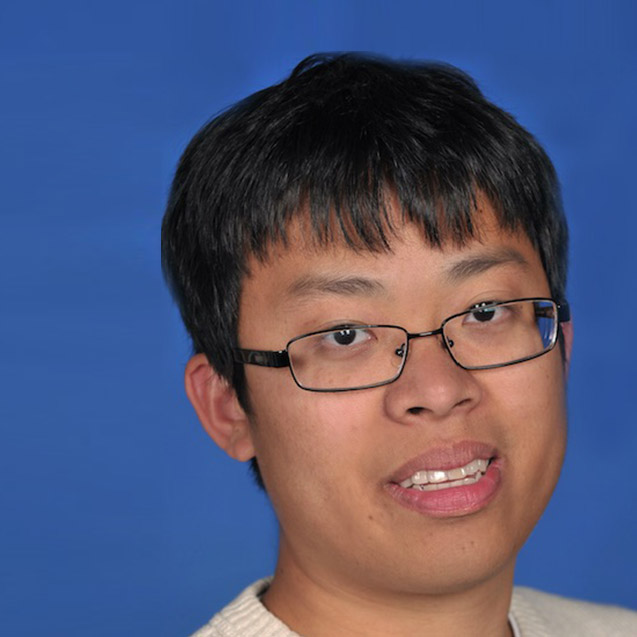
Bruce Dang is an information security enthusiast with interests in low-level systems. He is currently working at Veramine trying to make the world a safer place. He previously worked as a senior security development engineer lead at Microsoft; his team’s focus spans all things product-security related from hardware, OS, and web services. He specializes in reverse engineering and Windows kernel-level security projects. Before Microsoft, he worked as a developer in the financial sector. He was the first person to publicly discuss techniques of analyzing file format based exploits and has patents in the area of generic shell code and exploit detection. His public research includes Office exploit analysis, ROP detection, shell code detection, and kernel driver decompilation techniques; on the malware side, he is known for first analyzing vulnerabilities in the Stuxnet worm. He has spoken at major security conferences worldwide, i.e., REcon (Canada), Blackhat (Vegas and Tokyo), Chaos Computer Club (Germany), Computer Antivirus Research Organization (Hungary), etc. In addition to sharing his knowledge at public conferences, he has also provided private training and lectures to government agencies. He is also the co-author of the best-selling reverse engineering textbook, Practical Reverse Engineering: x86, x64, Windows kernel, and obfuscation , published by John Wiley & Sons.